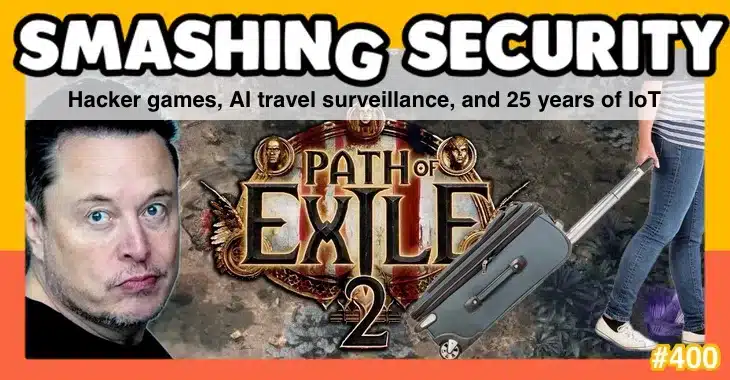
The online game Path of Exile 2 suffers a safety breach, we discover the problems of utilizing predictive algorithms in journey surveillance techniques, and the very worst IoT units are placed on present in Las Vegas. Oh, and has Elon Musk by chance revealed he cheats at video video games?
All this and far more is mentioned within the newest version of the award-winning “Smashing Safety” podcast by pc safety veterans Graham Cluley and Carole Theriault, joined this week by The Cyberwire’s Dave Bittner.
Warning: This podcast might include nuts, grownup themes, and impolite language.
Hosts:
Graham Cluley:
Carole Theriault:
Visitor:
Dave Bittner:
Episode hyperlinks:
Sponsored by:
Assist the present:
You possibly can assist the podcast by telling your folks and colleagues about “Smashing Safety”, and leaving us a assessment on Apple Podcasts or Podchaser.
Change into a Patreon supporter for ad-free episodes and our early-release feed!
Comply with us:
Comply with the present on Bluesky, or be a part of us on the Smashing Safety subreddit, or go to our web site for extra episodes.
Thanks:
Theme tune: “Vinyl Recollections” by Mikael Manvelyan.
Assorted sound results: AudioBlocks.



