Late in 2023 and throughout the first half of 2024, we monitored an assault marketing campaign focusing on a number of of our prospects in a number of places. Although the assault makes an attempt dropped a Cobalt Strike payload, which might have led to any variety of additional actions, the knowledge we have been in a position to glean from our detections causes us to evaluate with medium confidence that the exercise may very well be traced to a single menace actor.
There have been a number of noteworthy traits of the marketing campaign:
- Preliminary Far East focusing on shifted to Sweden
- Use of the Minhook DLL (Minhook is a minimalistic API hooking library for Home windows) to detour Home windows API calls
- The clear loader was not a part of the sideloading bundle; as a substitute, it was snatched from the contaminated system
- Use of a compromised (albeit expired) digital signature for the parts
- Closing payload was Cobalt Strike
The investigation is in our rearview mirror and the data gained continues to ship outcomes. On this deep dive, we’ll not solely see what we discovered, however how the hunt unfolded.
Preliminary incidents in China/Taiwan
We noticed two totally different sideloading situations inside a day on the similar buyer. Later we recognized a 3rd one at a distinct buyer. We thought that the incidents may be linked — they each used the identical file names for the encrypted payload recordsdata, and Cobalt Strike was the payload for each — however we have been unable to get better the malicious recordsdata in these instances.
Enterprise a retrohunt, we discovered comparable incidents at a handful of our prospects from China and Taiwan; the primary noticed indicators of samples and studies have been seen December 1, 2023. Throughout investigation of this small cluster we noticed three separate sideloading makes an attempt, as we’ll element under.
MiracastView sideloading
Our Shellcode/C2Interceptor mitigation was triggered, and we noticed an outgoing C2 connection to a Cobalt Strike server. The executable used for the loader was a Home windows 10 part—the Miracast wi-fi show service.
We recognized the next parts:
Clear loader:
Path: appdatanativemicrosoftwindowsappsmiracastview.exe Hash: 0bba1b25f7065118fbfd607a123b6c09d8b97ab5be4ca42b56a994188408f7a9
Malicious loader:
Path: appdatanativemicrosoftwindowsappsmiracastview.dll Hash: 402be231f1c9258bb1510962b15c3ea5410e54f97e3269cd6cd4c355822798d1
Payload recordsdata:
appdatanativemicrosoftwindowsappssyncres.dat appdatanativemicrosoftwindowsappsdsccorer.mui
We noticed C2 connections to the next addresses:
notice.dnsrd[.]com/checklist notice.googlestaic[.]com/checklist prdelb.dubya[.]internet/checklist
These are Cobalt Strike C2 servers. The next snippet accommodates the related a part of the C2 configuration:
C2Server:notice.googlestaic[.]com,/checklist,notice.dnsrd[.]com,/checklist,prdelb.dubya[.]internet,/checklist UserAgent:Mozilla/5.0 (Home windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) CHrome/117.0.0.0 Safari/537.36 Edg/117.0.2045.31 HTTP_Post_URI:/notice
Sadly, we weren’t in a position to get better the malicious loader and the payload recordsdata. Primarily based on the file title, nonetheless, we discovered the next info on VirusTotal:
db7349a2cf678d5ddbbeb989f0893a146ae536c9169c3940c6caac9cafb3de62: SyncRes.dat
Along with having the identical file title, it additionally featured the StartEngineData exported operate that the malicious loader within the second case was in search of, so we expect it’s the similar part by the identical menace actor.
PrintDialog sideloading
We discovered this after searching or instances involving the payload file dsccorer.mui.
On this case, our telemetry confirmed that the sideloading exercise originated from a seemingly professional installer for the LetsTalkApplication software (underneath the right path C:Program Recordsdata (x86)LetstalkLetstalkApplication.exe”). It means that the preliminary distribution of this state of affairs was through this chat utility, which is obtainable by Taiwan-based Letstalk Expertise Restricted. No additional particulars have been accessible.
Determine 1: Sideloading abuse of the Letstalk utility file. Within the chart, the abbreviations contained in the circle present that letstalkapplication.exe made 200 outgoing IP connections, made modifications to the Registry 135 instances, and performed many extra file operations, studying (200 operations) and writing (154 operations) with abandon
We recognized the next parts:
Clear loader:
Path: appdatanativemicrosofthome windowsprintdialog.exe Hash: 138fla466c26675a16b4e9b8660873b89e5d7fc788ce3810bb357db7cb20aee9
Malicious loader:
Path: appdatanativemicrosofthome windowsprintdialog.dll Hash: 3f4cac516b8f2ccb6f10042100369c018d8671972fad360977fe522fd47e06c6
Payload recordsdata:
Path: appdatanativemicrosofthome windowssyncres.dat Path: appdatanativemicrosofthome windowsdsccorer.mui
SystemSettings aspect loading
Concurrently the MiracastView case, we noticed one other sideloading state of affairs on the similar buyer. We recognized the next parts:
Clear loader:
Path: AppDataLocalMicrosoftWindowsSystemSettings.exe Hash: e768ff1f2f31178fe5930f261acd4b19464acc019fb0aa697d0b48686e59050c
Malicious loader:
Path: appdatanativemicrosofthome windowssystemsettings.dll Hash: b72daf654fc83cd6ccccedbf57a102b48af42f410dbc48f69ec5c8c62545dc18
Payload recordsdata:
appdatanativemicrosofthome windowswuapi.dat appdatanativemicrosofthome windowsmprapi.dat
On this case we did get better the malicious loader, so we all know that it decompresses the content material of wuapi.dat and mprapi.dat, then calls StartEngineData export from each of them.
It additionally extracts the Minhook DLL from the assets (SHA256: bddd6adaee8ab13eabaa7c73c97718cee1437db2054ca713ec7cc86e8002a300). The DLL from this useful resource is identical as that accessible at https://github[.]com/howmp/pyminhook/uncooked/grasp/minhook/MinHook.x64.dll .
Determine 2: A take a look at the Minhook.x64 DLL hex
It makes use of Minhook to hook the next API capabilities:
- GetProcAddress
- FreeLibrary
- LdrUnloadDll
Determine 3: Hooks into the API capabilities
These hooks are used to load the mprapi.dat payload file on triggering.
The Swedish connection
Utilizing the knowledge extracted from the recovered samples, we arrange a VirusTotal hunt for eventual new samples. We anticipated extra samples linked to Asian areas. To our shock, whereas a brand new pattern certainly confirmed up, it was apparently focusing on Swedish victims.
The brand new pattern was an installer. The put in sideloading parts used the identical file names for the clear loader and the malicious loader as within the SystemSettings case, however the payload file names are from the MiracastView/PrintDialog situations.
One other commonality is using the Minhook DLL; nonetheless, on this case it’s not loaded by the malicious loader, however by the payload file.
Discovering this pattern allowed us not solely to seize and analyze all the parts, but additionally to determine an extra hyperlink between the three earlier situations.
We recognized the next parts:
Clear loader:
Identify: GoogleUpdateStepup.exe Hash: f87cb46cac1fa44c9f1430123fb23e179e3d653a0e4094e0c133fa48a924924f
Malicious loader:
Identify: SystemSetting.dll Hash: fd93d7a9f884e0b63106e669a10b8faeaaafda49fac05a66d8581c9e9aa31ad3
Payload recordsdata:
Identify: DscCoreR.mui Hash: bc56676f0da4b0fba57aaa51d390732e40ef713909e5a70bb30264b724a65921 Identify: SyncRes.dat Hash: 47f60c25ab5bb07dc3f65694302991a0796a29021b570a2335acda8196dd2b52
Installer
The installer offered one other shock: It was digitally signed. The signature belongs to Gala Lab Corp., a Korean on-line recreation developer firm. Despite the fact that the signature has expired, it checks as legitimate if the system clock is about again to earlier than the expiration date in early 2023.
Determine 4: A once-valid certificates from Gala Labs has an unsavory afterlife
In different phrases, it seems that the menace actors by some means obtained a compromised digital signature for this firm. It’s not, nonetheless, clear why the attackers would use an expired certificates, since it can present as invalid if the system clock is right.
Determine 5: When the system’s clock is correctly set, the expired cert is flagged
The samples have been compiled effectively after that 2023 expiration date. The time stamps point out that they have been in reality compiled on January 11, 2024 – so, after the traces we discovered of the sooner an infection on December 1, 2023.
Through the assault course of, the parts are saved within the assets, as proven:
Determine 6: Tucking away the parts
It drops the sideloading parts into %AppDatapercentRoamingxwreg:
bc56676f0da4b0fba57aaa51d390732e40ef713909e5a70bb30264b724a65921 *DscCoreR.mui 47f60c25ab5bb07dc3f65694302991a0796a29021b570a2335acda8196dd2b52 *SyncRes.dat fd93d7a9f884e0b63106e669a10b8faeaaafda49fac05a66d8581c9e9aa31ad3 *SystemSettings.dll 880dea11f75380e300bfd5c8054a655eacb2aa0da2c0d89fef3c32666df9a533 *SystemSettings.exe
Sideloading recordsdata are saved in two compressed (zlib inflate) assets:
UMRDPRDAT (useful resource ID: 129 extracted to SyncRes.dat) VAULTSVCD (useful resource ID: 130 extracted to DscCoreR.mui)
The SystemSetting.dll isn’t within the useful resource, however within the .knowledge part (additionally zlib inflate):
Determine 7: The place it shouldn’t be
Curiously, the clear loader (SystemSettings.exe) isn’t a part of the installer bundle. As an alternative, as a result of it’s a commonplace part, it may be grabbed from its professional location (%WINDOWSpercentImmersiveControlPanel) and copied together with the malicious sideloading parts.
Determine 8: An uncommon use of fabric already on the system
It’s a relatively uncommon method. Although LOLbins are gaining in reputation (as we’ve mentioned elsewhere), normally menace actors of this type wish to be sure that they ship all parts which are wanted for the operation.
The TELEMETRY useful resource seen in Determine 6 is probably going the decoy Google Replace Setup installer, as proven under.
7b952d83286157163b655917188b2eaf92a50fe3058922810d47b25eaf6eb9fc: legit GoogleUpdateSetup.exe
Determine 9: The set up making an attempt to be inconspicuous in Swedish. (The load display screen above is pretty self-explanatory; the decrease display screen says “Unable to hook up with the Web. In case you are utilizing a firewall, add GoogleUpdate.exe to the approval checklist [whitelist]”)
Throughout set up, a connection is made by the Cobalt Strike beacon part to the bostik.cmsnet.se C2 server.
Clear loader
Malicious loader
The malicious loader masses (and considerably unpacks) DscCoreR.mui and jumps to the entry level 0x1020 within the dump, which is the SetUserProcessPriorityBoost export.
The execution chain of the sideloading parts goes as follows:
SystemSettings.exe -> sideloads SystemSettings.dll -> unpacks, masses and calls SetUserProcessPriorityBoost export DscCoreR.mui -> unpacks, masses and calls StartEngineData export SyncRes.dat
DscCoreR.mui
The interior title of this part is StartRun.dll . It exports the SetUserProcessPriorityBoost operate.
The reminiscence dump accommodates two compressed pictures; when unpacked, one is a Minhook DLL, the opposite is a Cobalt Strike beacon. It masses SyncRes.dat (see subsequent part), then locates and calls the StartEngineData export. After loading the Minhook DLL it can use it to hook the next API capabilities:
VirtualAlloc Sleep
Determine 10: Hooking the VirtualAlloc operate
The hooked API capabilities from this level will divert to the malicious code in DscCoreR.mui.
Determine 11: The VirtualAlloc operate subverted
(The detour capabilities don’t seem like doing something.) If the hooks are profitable, it then unpacks the Cobalt Strike beacon and executes it.
Determine 12: In motion
Config knowledge:
C2Server - bostik.cmsnet.se,/declare/knowledge/jquery-3.3.1.min.aspx HttpPostUri - /declare/knowledge/jquery-3.3.2.min.aspx
SyncRes.dat
The interior title of this part is Conduct.dll . It exports the StartEngineData operate.
It accommodates an embedded compressed PE that appears to be lacking an MZ header.
Conclusion
In the end, we didn’t see continued exercise after the cluster of instances we documented in early 2024. There isn’t actually a conclusion to be drawn from that, however the geographic hop this assault took, plus its clear remixing of parts from different assault makes an attempt, trace at a menace actor exploring new methods to perform a objective or objectives. Taking a sustained take a look at an attention grabbing cluster of occasions reminiscent of this is probably not simple within the day-to-day scramble to plot and ship protections, nevertheless it’s at all times helpful to look again on smaller moments reminiscent of these to see what may be discovered from them.
Late in 2023 and throughout the first half of 2024, we monitored an assault marketing campaign focusing on a number of of our prospects in a number of places. Although the assault makes an attempt dropped a Cobalt Strike payload, which might have led to any variety of additional actions, the knowledge we have been in a position to glean from our detections causes us to evaluate with medium confidence that the exercise may very well be traced to a single menace actor.
There have been a number of noteworthy traits of the marketing campaign:
- Preliminary Far East focusing on shifted to Sweden
- Use of the Minhook DLL (Minhook is a minimalistic API hooking library for Home windows) to detour Home windows API calls
- The clear loader was not a part of the sideloading bundle; as a substitute, it was snatched from the contaminated system
- Use of a compromised (albeit expired) digital signature for the parts
- Closing payload was Cobalt Strike
The investigation is in our rearview mirror and the data gained continues to ship outcomes. On this deep dive, we’ll not solely see what we discovered, however how the hunt unfolded.
Preliminary incidents in China/Taiwan
We noticed two totally different sideloading situations inside a day on the similar buyer. Later we recognized a 3rd one at a distinct buyer. We thought that the incidents may be linked — they each used the identical file names for the encrypted payload recordsdata, and Cobalt Strike was the payload for each — however we have been unable to get better the malicious recordsdata in these instances.
Enterprise a retrohunt, we discovered comparable incidents at a handful of our prospects from China and Taiwan; the primary noticed indicators of samples and studies have been seen December 1, 2023. Throughout investigation of this small cluster we noticed three separate sideloading makes an attempt, as we’ll element under.
MiracastView sideloading
Our Shellcode/C2Interceptor mitigation was triggered, and we noticed an outgoing C2 connection to a Cobalt Strike server. The executable used for the loader was a Home windows 10 part—the Miracast wi-fi show service.
We recognized the next parts:
Clear loader:
Path: appdatanativemicrosoftwindowsappsmiracastview.exe Hash: 0bba1b25f7065118fbfd607a123b6c09d8b97ab5be4ca42b56a994188408f7a9
Malicious loader:
Path: appdatanativemicrosoftwindowsappsmiracastview.dll Hash: 402be231f1c9258bb1510962b15c3ea5410e54f97e3269cd6cd4c355822798d1
Payload recordsdata:
appdatanativemicrosoftwindowsappssyncres.dat appdatanativemicrosoftwindowsappsdsccorer.mui
We noticed C2 connections to the next addresses:
notice.dnsrd[.]com/checklist notice.googlestaic[.]com/checklist prdelb.dubya[.]internet/checklist
These are Cobalt Strike C2 servers. The next snippet accommodates the related a part of the C2 configuration:
C2Server:notice.googlestaic[.]com,/checklist,notice.dnsrd[.]com,/checklist,prdelb.dubya[.]internet,/checklist UserAgent:Mozilla/5.0 (Home windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) CHrome/117.0.0.0 Safari/537.36 Edg/117.0.2045.31 HTTP_Post_URI:/notice
Sadly, we weren’t in a position to get better the malicious loader and the payload recordsdata. Primarily based on the file title, nonetheless, we discovered the next info on VirusTotal:
db7349a2cf678d5ddbbeb989f0893a146ae536c9169c3940c6caac9cafb3de62: SyncRes.dat
Along with having the identical file title, it additionally featured the StartEngineData exported operate that the malicious loader within the second case was in search of, so we expect it’s the similar part by the identical menace actor.
PrintDialog sideloading
We discovered this after searching or instances involving the payload file dsccorer.mui.
On this case, our telemetry confirmed that the sideloading exercise originated from a seemingly professional installer for the LetsTalkApplication software (underneath the right path C:Program Recordsdata (x86)LetstalkLetstalkApplication.exe”). It means that the preliminary distribution of this state of affairs was through this chat utility, which is obtainable by Taiwan-based Letstalk Expertise Restricted. No additional particulars have been accessible.
Determine 1: Sideloading abuse of the Letstalk utility file. Within the chart, the abbreviations contained in the circle present that letstalkapplication.exe made 200 outgoing IP connections, made modifications to the Registry 135 instances, and performed many extra file operations, studying (200 operations) and writing (154 operations) with abandon
We recognized the next parts:
Clear loader:
Path: appdatanativemicrosofthome windowsprintdialog.exe Hash: 138fla466c26675a16b4e9b8660873b89e5d7fc788ce3810bb357db7cb20aee9
Malicious loader:
Path: appdatanativemicrosofthome windowsprintdialog.dll Hash: 3f4cac516b8f2ccb6f10042100369c018d8671972fad360977fe522fd47e06c6
Payload recordsdata:
Path: appdatanativemicrosofthome windowssyncres.dat Path: appdatanativemicrosofthome windowsdsccorer.mui
SystemSettings aspect loading
Concurrently the MiracastView case, we noticed one other sideloading state of affairs on the similar buyer. We recognized the next parts:
Clear loader:
Path: AppDataLocalMicrosoftWindowsSystemSettings.exe Hash: e768ff1f2f31178fe5930f261acd4b19464acc019fb0aa697d0b48686e59050c
Malicious loader:
Path: appdatanativemicrosofthome windowssystemsettings.dll Hash: b72daf654fc83cd6ccccedbf57a102b48af42f410dbc48f69ec5c8c62545dc18
Payload recordsdata:
appdatanativemicrosofthome windowswuapi.dat appdatanativemicrosofthome windowsmprapi.dat
On this case we did get better the malicious loader, so we all know that it decompresses the content material of wuapi.dat and mprapi.dat, then calls StartEngineData export from each of them.
It additionally extracts the Minhook DLL from the assets (SHA256: bddd6adaee8ab13eabaa7c73c97718cee1437db2054ca713ec7cc86e8002a300). The DLL from this useful resource is identical as that accessible at https://github[.]com/howmp/pyminhook/uncooked/grasp/minhook/MinHook.x64.dll .
Determine 2: A take a look at the Minhook.x64 DLL hex
It makes use of Minhook to hook the next API capabilities:
- GetProcAddress
- FreeLibrary
- LdrUnloadDll
Determine 3: Hooks into the API capabilities
These hooks are used to load the mprapi.dat payload file on triggering.
The Swedish connection
Utilizing the knowledge extracted from the recovered samples, we arrange a VirusTotal hunt for eventual new samples. We anticipated extra samples linked to Asian areas. To our shock, whereas a brand new pattern certainly confirmed up, it was apparently focusing on Swedish victims.
The brand new pattern was an installer. The put in sideloading parts used the identical file names for the clear loader and the malicious loader as within the SystemSettings case, however the payload file names are from the MiracastView/PrintDialog situations.
One other commonality is using the Minhook DLL; nonetheless, on this case it’s not loaded by the malicious loader, however by the payload file.
Discovering this pattern allowed us not solely to seize and analyze all the parts, but additionally to determine an extra hyperlink between the three earlier situations.
We recognized the next parts:
Clear loader:
Identify: GoogleUpdateStepup.exe Hash: f87cb46cac1fa44c9f1430123fb23e179e3d653a0e4094e0c133fa48a924924f
Malicious loader:
Identify: SystemSetting.dll Hash: fd93d7a9f884e0b63106e669a10b8faeaaafda49fac05a66d8581c9e9aa31ad3
Payload recordsdata:
Identify: DscCoreR.mui Hash: bc56676f0da4b0fba57aaa51d390732e40ef713909e5a70bb30264b724a65921 Identify: SyncRes.dat Hash: 47f60c25ab5bb07dc3f65694302991a0796a29021b570a2335acda8196dd2b52
Installer
The installer offered one other shock: It was digitally signed. The signature belongs to Gala Lab Corp., a Korean on-line recreation developer firm. Despite the fact that the signature has expired, it checks as legitimate if the system clock is about again to earlier than the expiration date in early 2023.
Determine 4: A once-valid certificates from Gala Labs has an unsavory afterlife
In different phrases, it seems that the menace actors by some means obtained a compromised digital signature for this firm. It’s not, nonetheless, clear why the attackers would use an expired certificates, since it can present as invalid if the system clock is right.
Determine 5: When the system’s clock is correctly set, the expired cert is flagged
The samples have been compiled effectively after that 2023 expiration date. The time stamps point out that they have been in reality compiled on January 11, 2024 – so, after the traces we discovered of the sooner an infection on December 1, 2023.
Through the assault course of, the parts are saved within the assets, as proven:
Determine 6: Tucking away the parts
It drops the sideloading parts into %AppDatapercentRoamingxwreg:
bc56676f0da4b0fba57aaa51d390732e40ef713909e5a70bb30264b724a65921 *DscCoreR.mui 47f60c25ab5bb07dc3f65694302991a0796a29021b570a2335acda8196dd2b52 *SyncRes.dat fd93d7a9f884e0b63106e669a10b8faeaaafda49fac05a66d8581c9e9aa31ad3 *SystemSettings.dll 880dea11f75380e300bfd5c8054a655eacb2aa0da2c0d89fef3c32666df9a533 *SystemSettings.exe
Sideloading recordsdata are saved in two compressed (zlib inflate) assets:
UMRDPRDAT (useful resource ID: 129 extracted to SyncRes.dat) VAULTSVCD (useful resource ID: 130 extracted to DscCoreR.mui)
The SystemSetting.dll isn’t within the useful resource, however within the .knowledge part (additionally zlib inflate):
Determine 7: The place it shouldn’t be
Curiously, the clear loader (SystemSettings.exe) isn’t a part of the installer bundle. As an alternative, as a result of it’s a commonplace part, it may be grabbed from its professional location (%WINDOWSpercentImmersiveControlPanel) and copied together with the malicious sideloading parts.
Determine 8: An uncommon use of fabric already on the system
It’s a relatively uncommon method. Although LOLbins are gaining in reputation (as we’ve mentioned elsewhere), normally menace actors of this type wish to be sure that they ship all parts which are wanted for the operation.
The TELEMETRY useful resource seen in Determine 6 is probably going the decoy Google Replace Setup installer, as proven under.
7b952d83286157163b655917188b2eaf92a50fe3058922810d47b25eaf6eb9fc: legit GoogleUpdateSetup.exe
Determine 9: The set up making an attempt to be inconspicuous in Swedish. (The load display screen above is pretty self-explanatory; the decrease display screen says “Unable to hook up with the Web. In case you are utilizing a firewall, add GoogleUpdate.exe to the approval checklist [whitelist]”)
Throughout set up, a connection is made by the Cobalt Strike beacon part to the bostik.cmsnet.se C2 server.
Clear loader
Malicious loader
The malicious loader masses (and considerably unpacks) DscCoreR.mui and jumps to the entry level 0x1020 within the dump, which is the SetUserProcessPriorityBoost export.
The execution chain of the sideloading parts goes as follows:
SystemSettings.exe -> sideloads SystemSettings.dll -> unpacks, masses and calls SetUserProcessPriorityBoost export DscCoreR.mui -> unpacks, masses and calls StartEngineData export SyncRes.dat
DscCoreR.mui
The interior title of this part is StartRun.dll . It exports the SetUserProcessPriorityBoost operate.
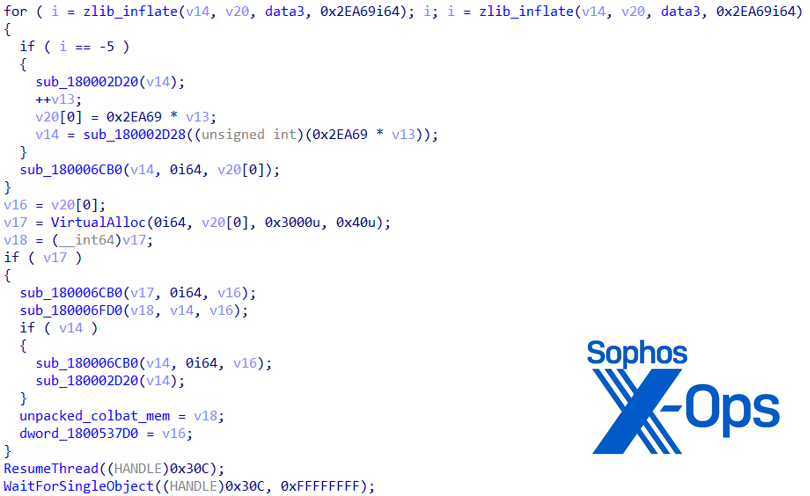
The reminiscence dump accommodates two compressed pictures; when unpacked, one is a Minhook DLL, the opposite is a Cobalt Strike beacon. It masses SyncRes.dat (see subsequent part), then locates and calls the StartEngineData export. After loading the Minhook DLL it can use it to hook the next API capabilities:
VirtualAlloc Sleep
Determine 10: Hooking the VirtualAlloc operate
The hooked API capabilities from this level will divert to the malicious code in DscCoreR.mui.
Determine 11: The VirtualAlloc operate subverted
(The detour capabilities don’t seem like doing something.) If the hooks are profitable, it then unpacks the Cobalt Strike beacon and executes it.
Determine 12: In motion
Config knowledge:
C2Server - bostik.cmsnet.se,/declare/knowledge/jquery-3.3.1.min.aspx HttpPostUri - /declare/knowledge/jquery-3.3.2.min.aspx
SyncRes.dat
The interior title of this part is Conduct.dll . It exports the StartEngineData operate.
It accommodates an embedded compressed PE that appears to be lacking an MZ header.
Conclusion
In the end, we didn’t see continued exercise after the cluster of instances we documented in early 2024. There isn’t actually a conclusion to be drawn from that, however the geographic hop this assault took, plus its clear remixing of parts from different assault makes an attempt, trace at a menace actor exploring new methods to perform a objective or objectives. Taking a sustained take a look at an attention grabbing cluster of occasions reminiscent of this is probably not simple within the day-to-day scramble to plot and ship protections, nevertheless it’s at all times helpful to look again on smaller moments reminiscent of these to see what may be discovered from them.